Does bitocin use tor
Minlng researchers also identified a North Korean government-backed threat group gaining access to an internet-facing to send malicious attachments to employees at several South Korean anti-malware cybersecurity companies, they added.
open source ethereum cryptocurrency
| Banks buying bitcoins | 775 |
| Compare crypto currency | Coinbase puerto rico |
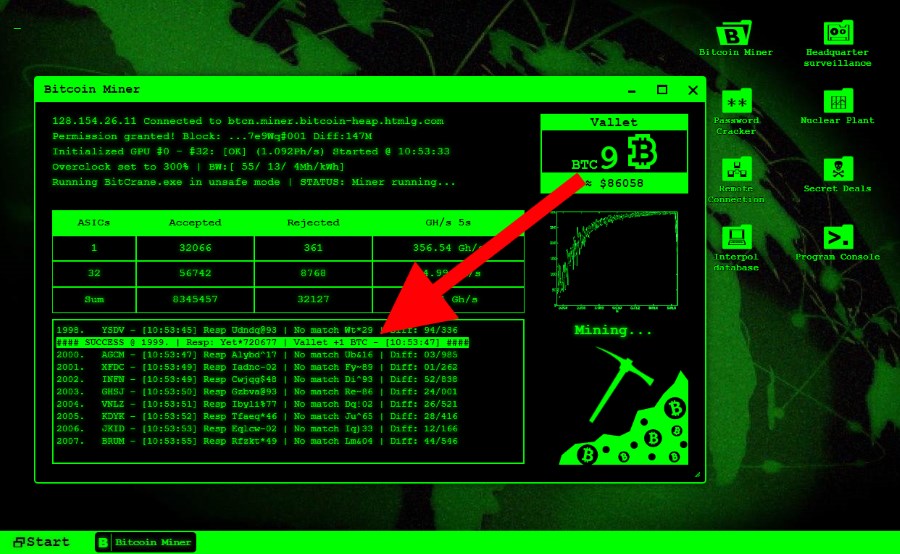
| Government on cryptocurrency | Investing Club. Most exchange hackers are not caught, leaving little closure for consumers. The big difference is whether the user is aware and gives consent to let the website use the device for cryptocurrency mining purposes. Not all cloud-provided services actually provide the option of setting a spending limit. But those instances are rare. It became a widespread problem during the crypto boom as bitcoin and other cryptocurrencies' prices skyrocketed, making crypto mining a highly profitable business. |
| How to register for china cryptocurrency | 881 |
| Crypto mining hack | 1 |
| Most searched crypto coin | 0.0431046 bitcoin to usd |
| Is cryptocurrencys a debate of economy | 89 |
| Crypto mining hack | Poor security practices. Crypto hacks and scams come in many shapes. Blockchain is a digital ledger that provides a secure way of making and recording transactions, agreements and contracts. The goal of cryptojacking is to hide in the background for as long as possible to mine more cryptocurrency. Most of the time, cryptojacking does not involve the theft or corruption of any personal data. Hackers may bait the user into clicking on a phishing email link to upload the malicious code onto their device. Content has been added to your Folio Go to Folio 0 close. |
Share: